Options
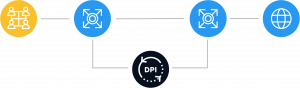
BNG
BASE
COMPLETE
Bypass, On-stick, LAG Support
Statistics by protocols and directions in IPFIX format collection and export
Traffic priority marking depending on the application protocol and direction
Channel policing and session policing, traffic priorities per channel
Subscriber channel policing and session policing, traffic priorities per subscriber
Allow Lists and redirecting to Captive Portal
BNG/BRAS L3 (IPoE), Dual Stack IPv4/IPv6, RADIUS with CoA
BNG/BRAS L2 (PPPoE, DHCP, L2TP), Dual Stack IPv4/IPv6
Router with BGP, OSPF, VRF support
Carrier Grade NAT with NAT Flow export in IPFIX format
Mini-Firewall for blocking by ports
Automatic protection against DDoS attacks
Regulatory Compliance
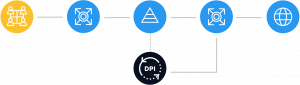
BNG
BASE
COMPLETE
Filtering by blocked Internet sites and blacklisting
Lawful Interception (LI), metadata export by IPFIX
Additional modules and services
BNG
BASE
COMPLETE
URL Classifier Local version
URL Classifier Cloud version
Graphical User Interface Base version
GUI (Graphical User Interface) FilterUI version
Quality of Experience Module Base version
Quality of Experience Module Standard version
SDK — DPI Tool kit for protocols customization
Subscription
VAS Cloud custom protocols
Subscription
Standby
BNG
BASE
COMPLETE
Active-Standby: the stand-by SSG is installed on an alternative route, passing no more than 5% of traffic in standby mode
25% from Main License and Support License
Active-Active: traffic is shared between two SSG platforms
100% from Main License and Support License