
From the days of dial-up (many remember that familiar modem noise) to fiber to the building (FTTB/FTTH) and Wi-Fi, no less than 20 years have passed, and data transfer speeds have increased from 0.1 Kbps to several Gbps, which places certain demands on network operation and the equipment used.
The bandwidth of a telecommunications operator is not infinite
Network bandwidth is not infinite — this is a fact and a fundamental principle both in the construction of a provider’s network or an organization such as a factory or plant, and in the use of hosting services. The bandwidth of a communication line depends on its characteristics — attenuation and speed — as well as on the spectrum of signals transmitted over it. Wireless networks can be considered as a specific example — signal attenuation depends on the distance and transmitter power, and the data transfer speed depends on the number of clients on a single channel. Another example, familiar from school, is a local area network: if there is one client and one server on the network, there seems to be no problem; two clients and one server will share the bandwidth in half, and so on.
What network traffic consists of
To use bandwidth rationally, you need to understand what traffic exists on the network and know how critical it is to latency. In a provider’s network, all traffic can be divided into two types: user traffic and service traffic. Service traffic consists of information for user authentication and accounting, network monitoring, DHCP and DNS service traffic, and other traffic. User traffic is essentially all other traffic: HTTP/HTTPS data, text, voice, and video messaging data, streaming video, online service traffic, torrent traffic, and so on. The share of service traffic in the provider’s network does not exceed 1%. All uplink, computing power of network equipment, and bandwidth of the telecom operator’s local network itself are spent on customers.
If we look at the network not from the provider’s side, but from the side of a user who owns a website or a small organization, the picture will be slightly different. The website owner’s traffic will consist mainly of HTTP requests, responses to them in the form of page data returned by the server (website pages, associated scripts, styles, images, etc.), and service information.
The organization’s traffic will be somewhat similar to user traffic—email, voice and video data, website server responses, various types of information for internal use, and the organization’s applications.
We should not forget about the types of DDoS attacks, when the channel is filled with traffic transmitted to the network for a particular node, or when several thousand clients suddenly connect to the organization’s servers (for example, web). In this case, the communication channel may be 100% full.
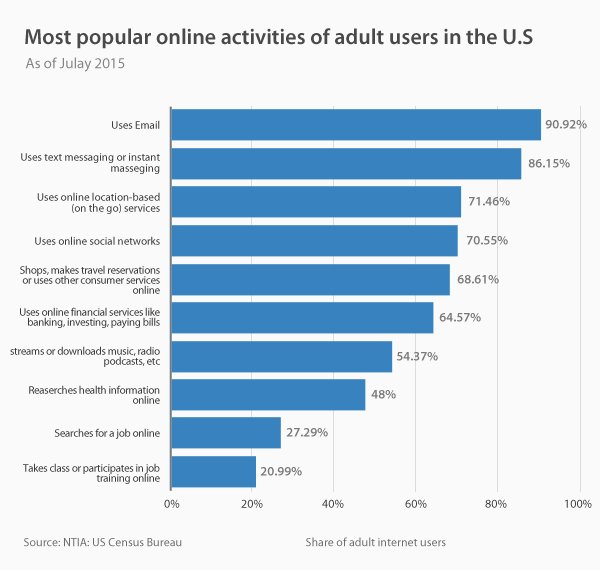
According to statistics, the most popular online services among the adult population of the United States are email, followed by text or instant messaging. Social networks rank fourth in this rating, with online education closing out the list.
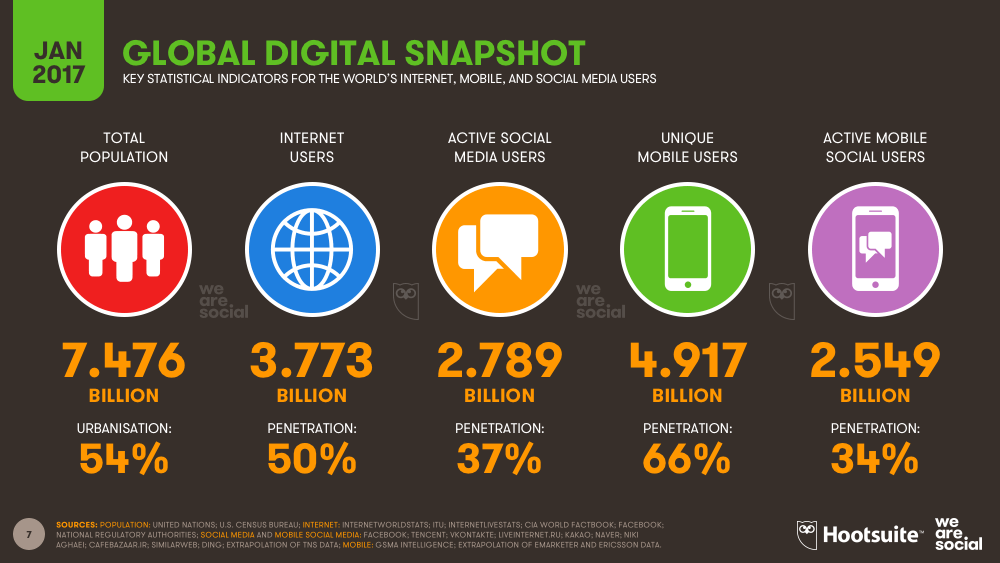
According to Hootsuite and We are social, as of January 2017, there are 7.4 billion people in the world, half of whom are Internet users. Two out of three people use mobile access.
Thus, the issue of optimizing the use of channels and resources to provide a given quality of service is of paramount importance.
Tools for saving bandwidth
What to do if the communication channel is almost full?
The first option for solving the problem is, of course, to increase the width of the communication channel. But sometimes this is impossible or too expensive even for corporate clients. In this case, it makes sense to reduce the amount of data transmitted in the communication channel. There are several ways to do this.
For website owners, the right solution would be to cache static files and compress website pages—all of which can be done in the web server settings. It also makes sense to pay attention to image optimization and the use of CDN technology.
For providers and organizations with a large enough network, in addition to the above, to save bandwidth, you should consider using a standalone caching server or caching proxy server. It is also worth considering data compression within the network, for example, using the MPPC (Microsoft Point-to-Point Compression) protocol.
Data compression, thin clients, caching, and traffic optimization solutions can sometimes reduce traffic by 2-5 times (traffic from different applications is compressed differently). It is also important to understand the traffic structure and how the communication channel is actually used. This can be done, for example, with Flow technologies. Then use traffic prioritization methods to reduce possible packet loss and queue growth in active equipment.
Combining QoS and bandwidth savings
QoS (Quality of Service) is a set of methods for managing packet network resources. It should be noted right away that QoS mechanisms are implemented differently in various network devices and operating systems: when the maximum is reached, packets can either be discarded or delayed. Since it is too costly to “collect” a queue of packets under heavy loads, packets are usually discarded.
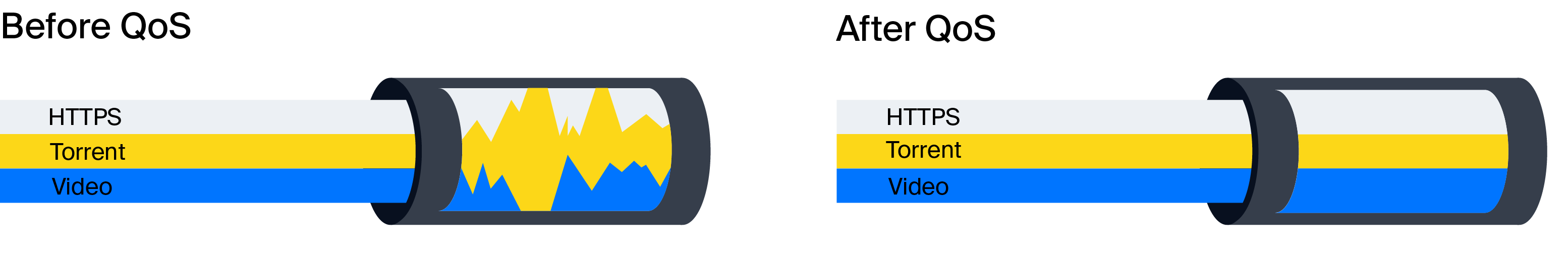
QoS tools can be used in cases where there is an application that requires a strictly defined bandwidth, such as video conferencing or VoIP. This method of traffic saving will work when there is activity. In other cases, the bandwidth reserved for this application becomes available for other purposes.
Traffic analysis and management for QoS
Today, the issue of traffic savings is still quite relevant. Despite the rapid development of technologies and the availability of network interfaces with a bandwidth of 100G, as well as their possible aggregation, it is worth remembering that bandwidth is not infinite. There are not many systems on the market that are capable of at least caching traffic. Most systems capable of independently prioritizing traffic do not have the ability to make operational changes to the configuration. Some of the most popular systems are those that analyze and manage traffic using DPI technology. These software and hardware complexes allow you to:
- Limit bandwidth for customers according to their tariff plan.
- Prevent network congestion, ensuring the quality and speed of Internet access.
- Prioritize traffic at all stages of delivery to the user.
- Reduce uplink costs and improve QoE.
- Control the upper limit
- Counteract DDoS attacks.
Despite their wide range of functions, such systems have flexible settings and are easily integrated into the network of a telecommunications operator or Internet service provider.
