
In the process of standardization by the IETF organization, QUIC was divided into transport and HTTP protocols. Using the transport QUIC, not only HTTP data is transmitted, but also other data — the QUIC Working Group is engaged in this development.
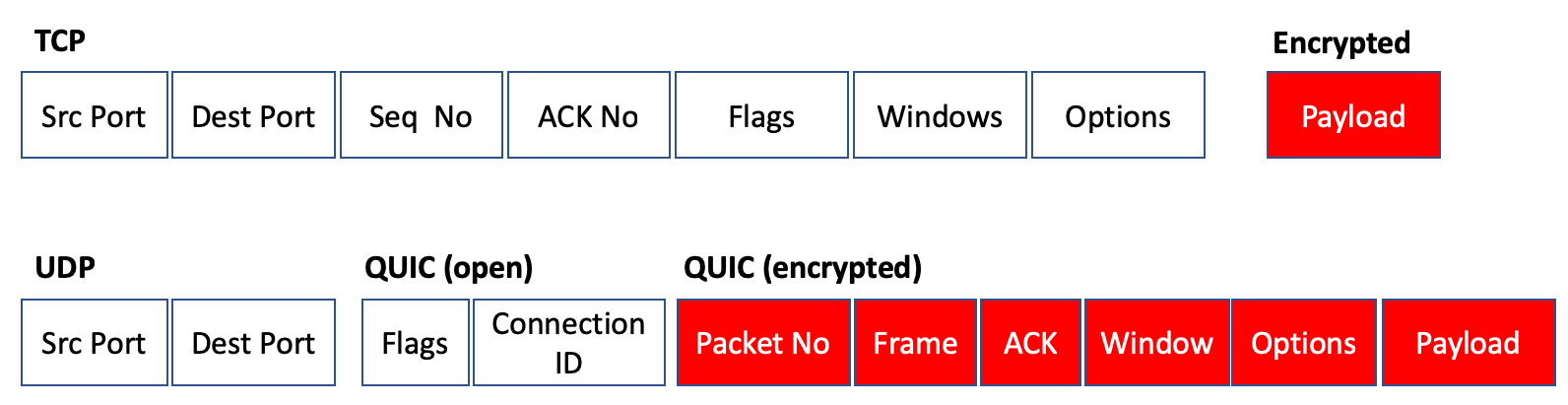
QUIC implies mandatory encryption of traffic: to do this, it uses TLS 1.3 to set session keys, and then encrypt each package. But since it is based on UDP, much of the session information and metadata open in TCP is encrypted in QUIC.
How Stingray SG processes QUIC
Before QUIC appeared, the detection of encrypted HTTPS connections took into account the SNI (Server Name Indication), which was transmitted in clear form when the client contacted the server.
The QUIC standard from the IETF introduces SNI encryption, which complicates the detection of the host to which the connection is being made. Since version 11.2 of Stingray SG, SNI decryption has become available when establishing a connection using the QUIC IETF protocol. This feature made it possible to split the QUIC IETF protocol connections into separate signatures, for which QUIC is the transport.
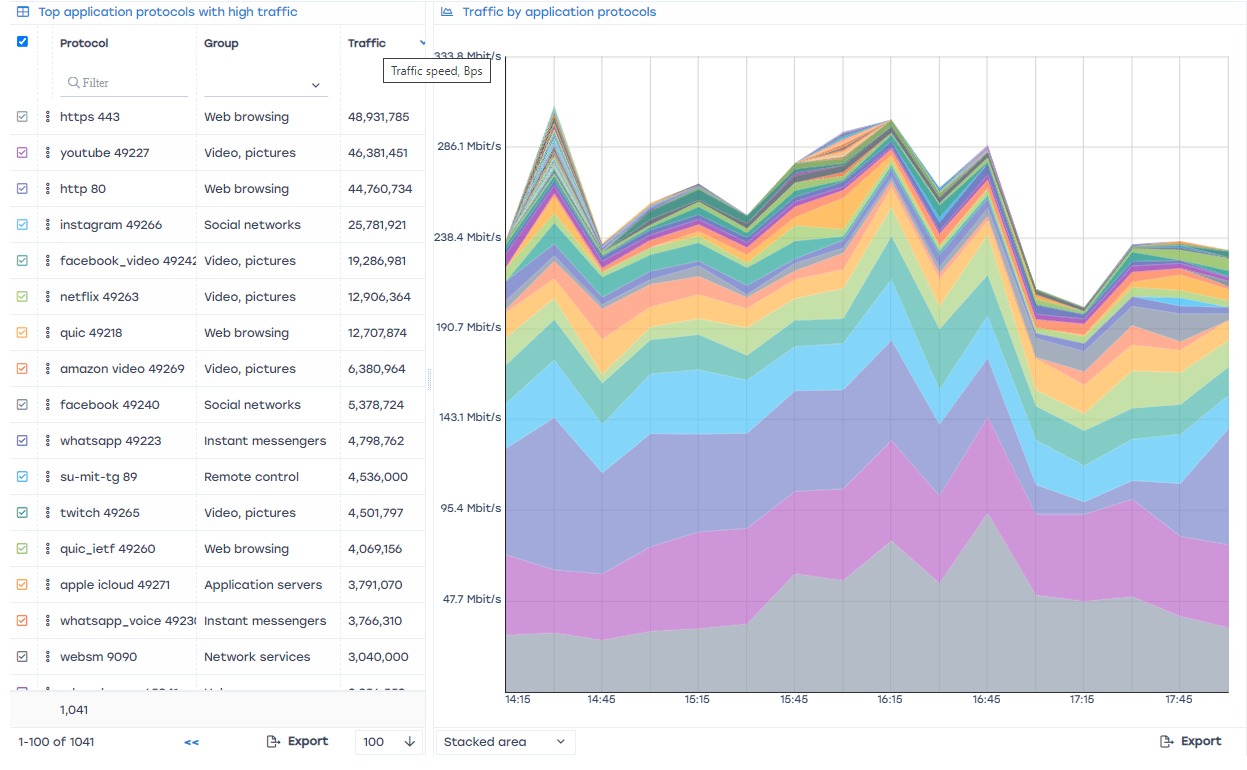
We see that both HTTP/HTTPS and QUIC/QUIC IETF protocols are present in the common channel. This tells us that there is a smooth transition to new standards. The allocation of applications that are based on these protocols is carried out by the name of the host domains on which the content is located, for example, YOUTUBE, TWITTER, FACEBOOK, INSTAGRAM.
Stingray SG signatures
Signatures mean traffic search patterns that are loaded into the DPI engine. They are used for constant scanning of all IP packets in order to determine whether Flow (IPscr:port — IPdst:port) belongs to a particular application/protocol/signature.
Signatures in Stingray SG are divided into two groups:
- Common
- Custom or Programmable.
Common signatures
Added and modified only by VAS Experts developers. They are loaded into the Stingray SG when the version of the Stingray SG software is updated.
Custom signatures
They are added by the user via the GUI Stingray SG using a personal account in VAS Cloud.
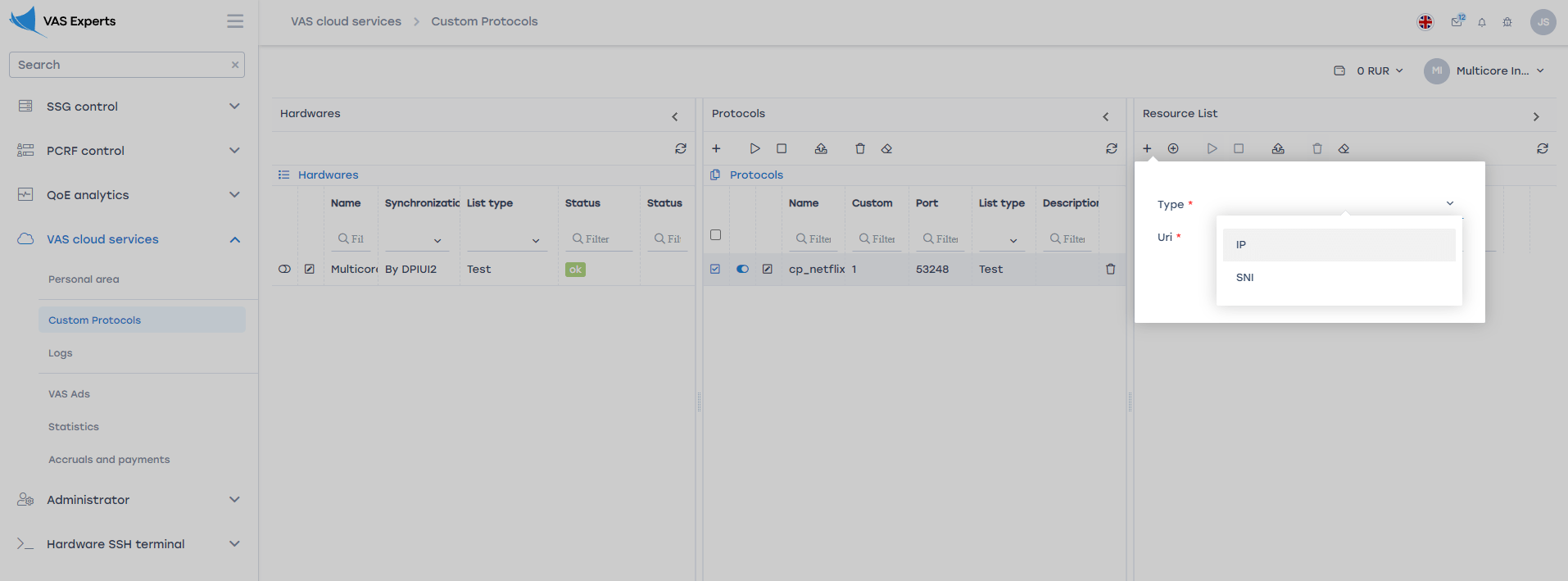
The custom signature is determined by the IP or domain name of the host (SNI) with which the user interacts. All Flow with these parameters are marked with the appropriate signature, in the future it can be defined in one of the eight policing classes, skipped without processing or blocked.
