
So when smartphones and smartwatches with e-SIM were released, the technology from 2016 has become a worldwide trend. Today, you can obtain e-sim services in 45 countries; in many others, the operators have doubts while the regulatory mechanism and technological platforms are not ready.
What is the doubt?
What is a SIM card? Basically it is a microcomputer with the main objective to keep keys and encryption algorithms used to identify and authenticate subscribers in the mobile operator network. The algorithms are symmetric and involve storage of the user’s secret key in a protected area of the SIM chip memory, which can only be accessed by an application running on the chip itself. Entire encryption algorithms (which are actually applications running on the SIM-Chip) and encryption keys are recorded during production to ensure their security.
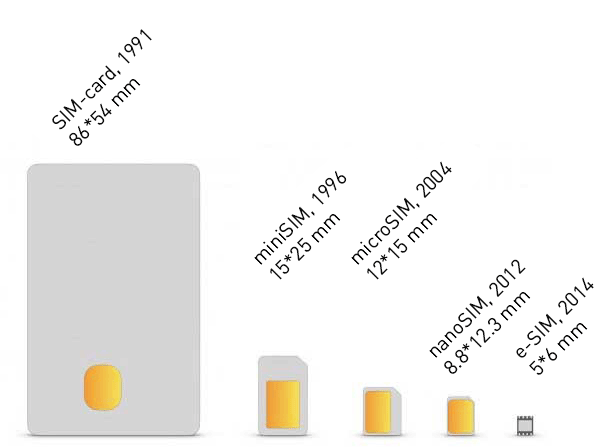
SIM-card evolution
There are other apps on SIM such as the SIM menu, which show weather forecasts, balance, etc., and can manage some services. Moreover, the operator can set a standardized option to download and run new applications on SIM, while the subscriber can be unaware of it. Without delving into the specifications and standards, we can notice this in the service of copying Contacts from a SIM card to the operator’s storage: the service is activated via the subscriber’s account on the operator’s website, and after a while, a backup copy of the Contacts is already created in the cloud. Magic? Thus, the operator has access to the subscriber’s device via SIM card and can receive data from this device and complete some operations with it… To provide quality services, of course. Learn more about how it works.
What is e-SIM (e-UICC)?
Contrary to common belief, the main difference from SIM is not the solder chip form factor (you can also buy the classic SIM in embedded form factor from operators), but pre-installed software that allows you to download subscriber profiles with encryption keys. This process is standardized by GSMA, an association of GSM operators and manufacturers, and is described in several specifications:
- SGP.21 «RSP Architecture»
- SGP.02 «Remote Provisioning Architecture for Embedded UICC Technical Specification»
- SGP.22 «RSP Technical Specification»
Another difference is that you need a third party to download the operator profile to e-SIM: SM-DP – a GSMA certified organization that will manage the profiles. It can be either a manufacturer of devices with built-in E-UICC or an independent company. Detailed description of e-SIM from GSMA.
Several conclusions:
- Operators are losing control over built-in SIM applications. Accordingly, they are losing the source of detailed data about subscribers. To compensate for this somehow it is possible to download and activate the profile on e-SIM using a separate application in the device itself, which will additionally transmit this data.
- Any cryptographic application may have undocumented features, as well as vulnerabilities. If such flaws give an attacker the ability to steal or modify operator profiles, then two-factor authentication technologies, mobile banking, and other critical services will become vulnerable. And in the given specifications, flaws were found and partially fixed, but who guarantees the future?
- The operator becomes dependent on a third party concerning subscriber relations. A third party may conspire with a competitor or sabotage the download of certain profiles on e-SIM for their selfish purposes.
- The encryption algorithms are controlled by the chip manufacturer, which now doesn’t work by order of the operator, but according to the GSMA specifications. Such standards may not match governmental requirements in a given country.
- Surely marketers and product managers will create new services based on the quick sale of virtual SIM cards. For example, a one-time package number + instant messengers for those who need to sell something and don’t want to give their main phone number. In other words, “Marketing wars” can give rise to previously impossible and completely new offers.
The comparison of classic SIM and e-UICC gives an understanding that the latter is more focused on improving service and developing new lines of product in the industry. There are a lot of amenities for subscribers: for example, you can remotely connect to a foreign operator before leaving the country. When arriving abroad, it remains just to activate a new profile in a couple of clicks instead of searching an operator’s sales point. For those who consider two SIM cards are not enough, it becomes possible to use 3-4 profiles and to switch between them as needed.
The presence of a third party is already being observed in the process of MNP – number transfer between operators. Today there are no critical problems in this regard. All operators were obliged to connect to the system – the system works, numbers are transferred. In general, it doesn’t cause challenges for anyone.
In conclusion, the e-SIM technology evokes mixed feelings. On the one hand, positive: this is a new step in the industry. On the other hand – there is another potential channel for the leak of personal and critically sensitive data from user devices.
