
One cannot really imagine a modern person having no access to the Internet. Message exchange, watching video files, listening to music, and much more is impossible without using network protocols the main one is the well-known Internet Protocol also abbreviated as IP or TCP/IP. Let’s consider the problems and prospects of its sixth version – IPv6.
A short historical background
The Internet Protocol was created in 1981 in order to “join the network segments into a single network providing the data packets transmission between any network nodes through an arbitrary number of intermediate routers” — from the protocol properties. Initially, the class addressing scheme was used, but as the Global Network rose it became inefficient due to irrational and wasteful usage of IPv4 resources since there was no possibility to use arbitrary subnet masks to different subnets. Eventually, the problem was solved by using the Classless Inter-Domain Routing (CIDR, pronounced “cider”), which implied the usage of a subnet mask. IPv4 is 4 octets of 8 bits each, so the total number of addresses is not infinite and is only 2^(4*8) = 2^32 = 4,294,967,296 addresses being available, which corresponds to a subnet of 0.0.0.0/0. According to RFC1918, the following networks: 10.0.0.0/8, 172.16.0.0/12, and 192.168.0.0/24 were “given away” for private needs and subsequently became known as gray, since they are not routed within the Global Network.
There were more and more network devices and the pool of available IP addresses gradually run out. Providers having a small address pool (that is, they have more clients than the white addresses available to be assigned to) have started to use dynamic IP assignments with strict session logging. Other providers started to use temporary solutions represented by NAT (network address translation) technology allowing to assign one white address for the whole gray subnet.
On February 1, 2011 the last 2 blocks /8 (subnet mask 255.0.0.0, the maximum number of hosts 16 777 216) were assigned to . The need to migrate from IPv4 to IPv6 has become acute to a lot of users.
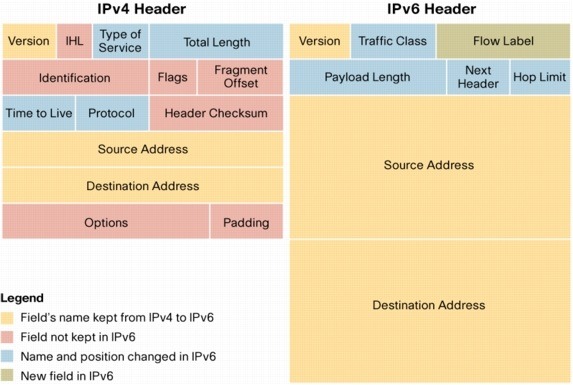
Figure 1. IPv4 and IPv6 packet headers comparison
IPv6, reasons for its implementation and prospects
IPv6 is a new version of the widely known IP protocol (also called IPv4). Its commissioning was marked by the World IPv6 Launch event occurred on June 6, 2012 after numerous tests and improvements.
Rationale for such a commissioning was the assignment of the last IPv4 addresses blocks to regional registrars by IANA. According to the creators, there should be a smooth transition from IPv4 to IPv6, and the need for IPv4 will eventually fade away thanks to double stack technique usage. The dynamics are shown in Figure 2, presented by Geoff Huston.
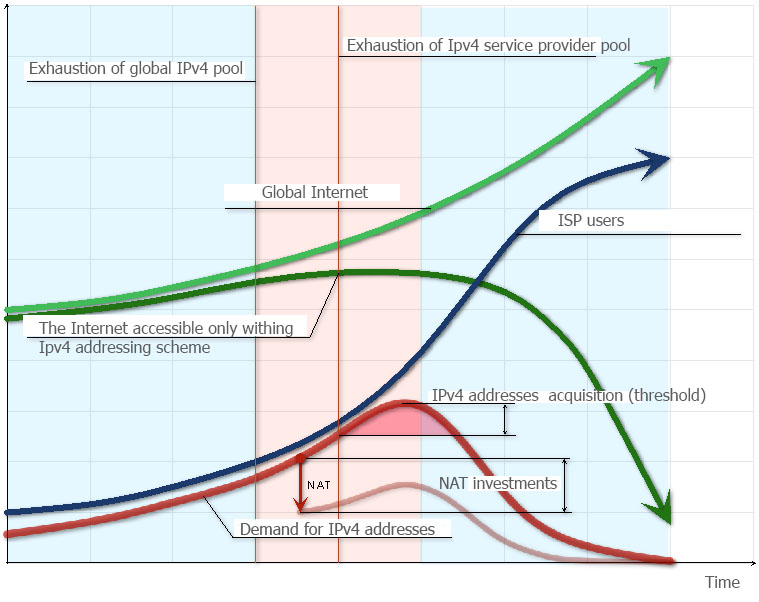
Figure 2. The dynamics of the IPv4 and IPv6 coexistence. Source (In Russian).
All well and good, but only in the figure above. This project, like NAT multiplexing, proved to be a failure. Indeed, the future has come, but many proved to be unprepared for this transition from IPv4 to IPv6.
Let us consider IPv4 to IPv6 transition challenges and possible ways to overcome them
The first and the main problem is understanding and adoption of new standards. From a human perspective, it is, first and foremost, the readability of network address and its understanding. It is no secret that information technology newcomers firstly associate the network address with the physical one of a network interface card (MAC address) differing by “only the higher number of digits/groups”. Approximately the same way the information was accepted by experienced specialists when the initial rumors about IPv6 have started. The usual 127.0.0.1 loopback address would be :: 1 in the IPv6 format. Particular attention should be given to the dual-format used within the mixed IPv4 and IPv6 environments. IPv6 plus IPv4 format (dual) is y:y:y:y:y:y:x.x.x.x, here y‘s are the hexadecimal values of six 16-bit address segments (any hexadecimal value between 0 and FFFF) separated by colons and x‘s are the decimal values of four 8-bit address octets (standard representation of IPv4 address) separated by dots. Ultimately, the problem of personnel training is soluble. Significant challenges are faced in terms of newer and obsolete device interconnection. And that is why.
Devices acquired prior to 2012 do not have IPv6 implementation either at the software or hardware level (operating systems are not taken into account). The information exchange between such devices is simply impossible. Moreover, the equipment having been suddenly obsolete is still working in many providers’ networks. Switches and routers replacement with newer ones is quite a costly procedure. In addition, the software for obsolete equipment is simply not being developed.
Even the software IPv6 stack Implementation would be impossible and would result in an increase in CPU load and in RAM usage due to hardware equipment limitations.
Availability of IPv6 networks from IPv4 ones and vice versa
The second problem arises from the first one, i.e. impossibility of communicating between devices using the different IP protocol versions. IETF offers several solutions, but they all boil down to using IPv4 tunnels and a dual-stack. Let’s consider some of them.
6to4 — in order to provide connectivity to the global IPv6 Internet, the so-called 6to4 relays are used. They are 6to4 gateways, providing an interface between 6to4 networks and the rest of the IPv6 Internet. An important limitation is the lack of control over the relay and consequently, it becomes impossible to guarantee the quality of communication. Despite its popularity, it is used mainly in small corporate networks.
6rd — solves the problem of getting access to IPv6 provider’s users without IPv6 support in the provider’s network, since it uses its own IPv6 address space and the entire 6rd service area is limited by the provider’s network.
DS-lite — implies that the provider’s network fully supports IPv6, but uses IPv4 tunnels to access its resources. The bottom line is to use a centralized NAT or CG-NAT. Communication with the IPv4 network is implemented through multiplexing, the access to the IPv6 network is implemented without using NAT. This scheme does not use protocol translation.
NAT64 — is applicable only in case the transition to IPv6 happens and in case the access to IPv4 networks would still be essential. The need for IPv4 to IPv6 access is also taken into account. Stream multiplexing is necessary, however there is no need for traffic tunneling. Interconnection of two networks happens transparently, but another problem with the DNS support appears: in some cases, the IPv4 address will be returned, and in others — the IPv6 one. This is addressed through the use of the ALG application server allowing to replace the IPv4 address with IPv6 one.
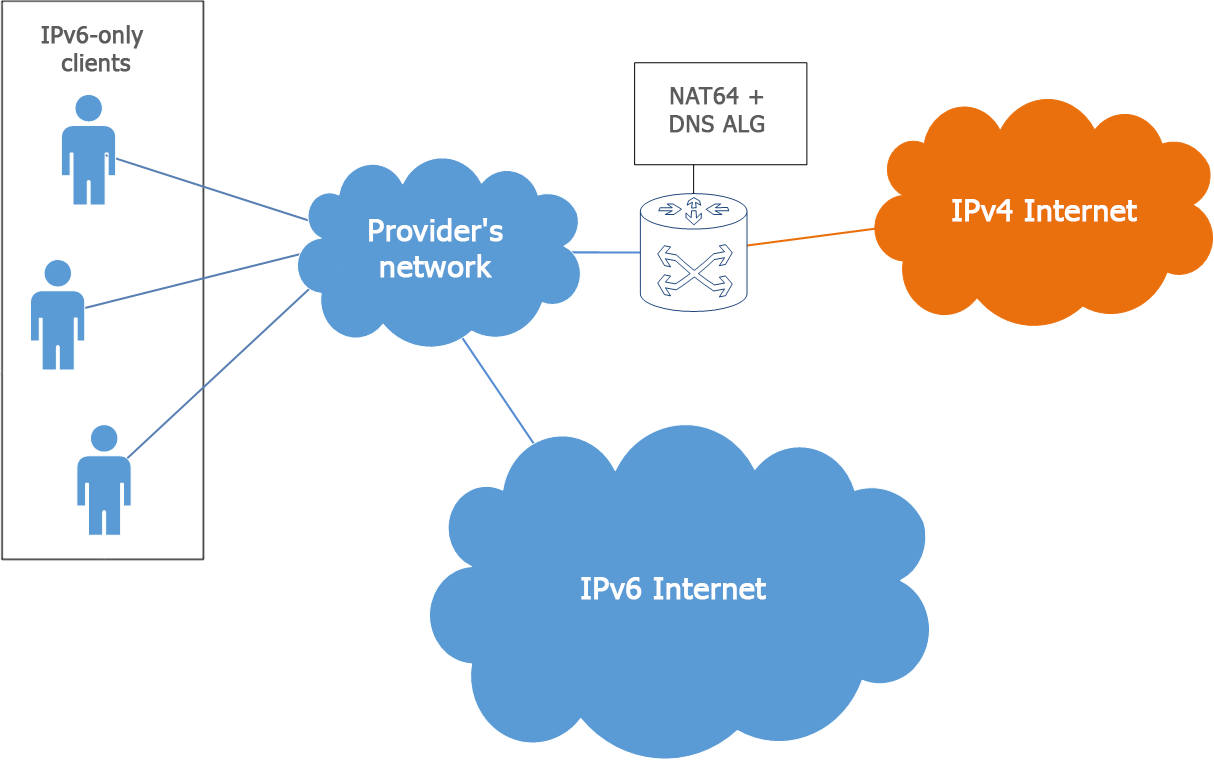
Figure 3. NAT64 + DNS
Despite the promise and ease of use of NAT64 and NAT in general, a third problem appears.
NAT does not solve all the problems
Given that all transitional methods are based, to varying degrees, on the use of NAT and the total number of Internet users is steadily growing (statistics can be viewed here), the question of the challenges faced when using the network address translation arises. Here are some of them:
Quality of communication may decrease due to packet fragmentation. Additional NAT devices could cause additional delays.
User identification will become more complex since one address can correspond to several users.
Functionality of applications could be impossible due to their special network features such as connections using strictly defined ports being assigned from well-known ports range. In a smaller network, one could use PAT (Port Forwarding) and again one time only.
Certain factors can affect safety. A DDoS attack on one IP address will affect the network segment behind it. The reverse alternative — an attack from one of the clients of the network will negatively affect the sanctions applicable to the entire segment. But one should not forget, that limitation on the use of ports for a user or for an application can lead to a greater probability of the DDoS attack.
IPv6 advantages
In the background of disadvantages mainly related to the IPv4 -> IPv6 transition challenge, rather than its maintenance, IPv6 has several advantages over IPv4.
The first and, undoubtedly, the most important advantage is the huge address space. The number of IPv6 addresses is 1028 (2128/232) times greater than the number of IPv4 addresses.
Theoretically 340,282,366,920,938,463,463,374,607,431,768,211,456 addresses are available. This means a density of about 6.67 * 10 ^ 27 IPv6 addresses per square meter of our planet.
Another important feature is the IP addresses autoconfiguration. This has been possible thanks to the SLAAC (Stateless Address Autoconfiguration) technique. It can be used both in conjunction with DHCP or individually. The SLAAC principle is that when creating a network, you specify the gateway address and the network prefix. This is enough to provide network devices with IP addresses. Configuration information is sent by the router every 200 seconds to the multicast address FF02::. Such packages are referred to as the Router Advertisement (RA).
Simplifying of routing — the introduction of the “Flow Label” field in the IPv6 protocol greatly simplified the procedure for routing a homogeneous packet flow. In addition, it is expected to simplify multicast transmission. It should be noted that the protocol defines a new address type referred to as anycast , so the packet is sent to the anycast address will be sent to the nearest interface from the address list. Routers can store only aggregated network addresses within their tables, which reduces the average size of the routing table to 8192 entries.
Removing redundant packet fields — Figure 1 shows that the packet header does not contain redundant fields. Although the packet size has become larger, it is easier to handle by the router. Information transmission becomes more efficient.
Quality of services support (QoS) is a new field defining the criteria the packet route between the source and destination will be chosen for. Using this field allows the routers to identify and provide special handling of packets related to this logical connection. Since the traffic is identified in the IPV6 header, the QoS support can be provided even in case the packet payload is encrypted by IPSec.
Crypto protection capability and enhanced data transmission security — the IPsec protocol allows encrypting any data (including UDP) without the need for any support from the application software side.
Is a transition from IPv4 to IPv6 worth the effort?
At the time of this writing, most devices are already compatible with IPv6. In any case, operating systems and modern routers have supported the standard implementation of this protocol. However, as already mentioned, telecom operators have a significant amount of “obsolete” equipment in their networks. There is no urgent need to switch to IPv6. Dual-stack technology will be used for a long time, but the IPv4 -> IPv6 transition fact is inevitable.
We, as a professional developer of solutions for telecommunication operators (DPI, BRAS, Communications Monitoring System), are always open in our desire to meet customer requests, so we are constantly modifying and improving our products. The latest versions of the Stingray Service Gateway provide the IPv6 support, and in the near future we will present a new release supporting Dual Stack (traffic shaping, services, termination, address assignment) and NAT technology.
For more information on the advantages of the modern deep packet inspection system — the Stingray Service Gateway, its effective usage within telecommunication operator networks, and also about migration from other platforms, please refer to specialists of the VAS Experts.
